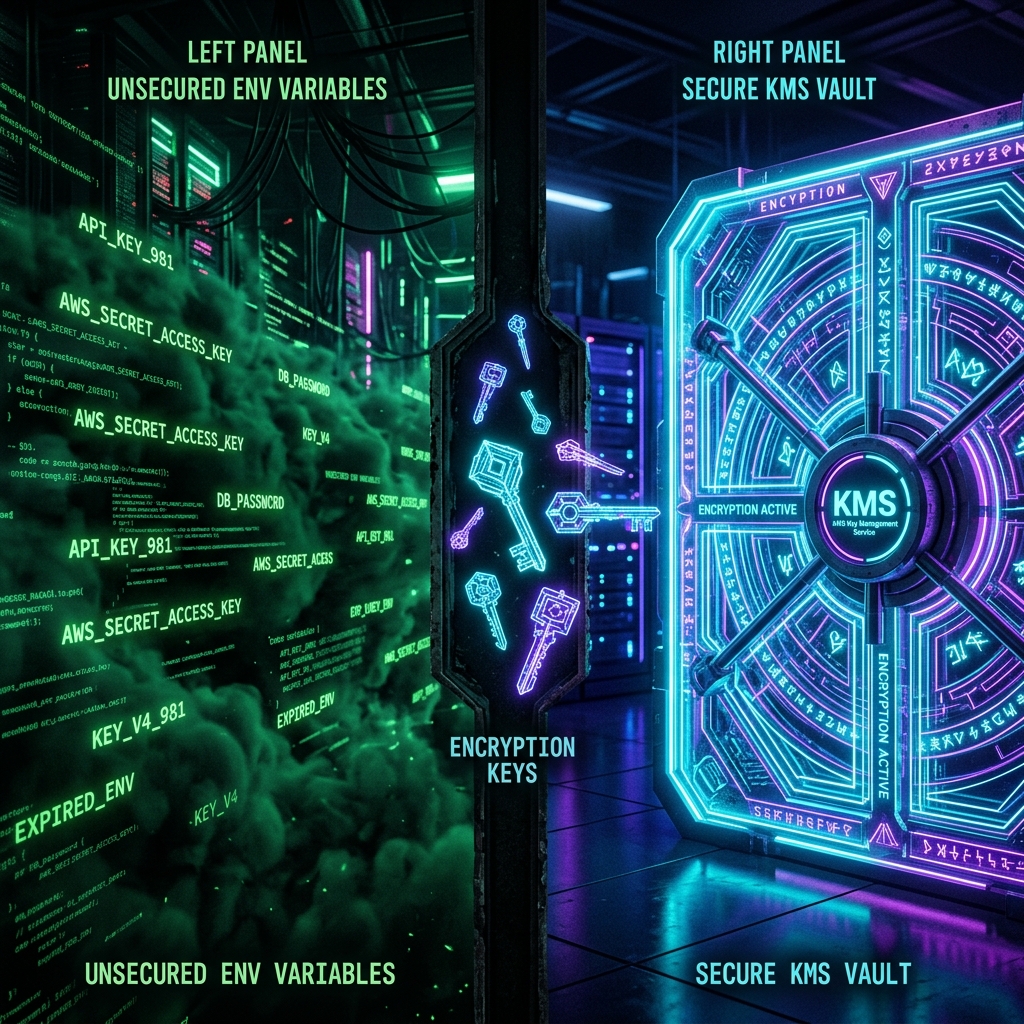
In the high-velocity world of 2026 CI/CD, the way we handle secrets defines the boundary between a robust pipeline and a catastrophic leak. For years, the industry baseline was the humble environment variable. But as our infrastructures scale and our threat models evolve, the choice between environment variables and a dedicated Key Management System (KMS) has become a defining architectural decision.
The Environment Variable Trap
Environment variables (process.env in Node, os.getenv in Python) are the path of least resistance. They are natively supported by almost every runtime, container orchestrator, and CI tool. However, their simplicity is their greatest security flaw.
Secrets stored as environment variables are often logged accidentally by debugging tools, visible to all processes in a container, and persistent in memory longer than necessary. In a GitHub Actions context, while "Secrets" are masked in logs, they are still injected into the runner's environment, where a single malicious dependency or a misconfigured step can exfiltrate them.
# Example of the 'Old Way' - Injecting secrets as env vars
steps:
- name: Deploy
env:
DB_PASSWORD: ${{ secrets.DB_PASSWORD }} # Risky persistence
run: ./deploy.shThe KMS Paradigm: Workload Identity Federation
By 2026, the standard has shifted toward Workload Identity Federation via OpenID Connect (OIDC). Instead of injecting a long-lived secret like an AWS Access Key into your GitHub runner, you configure your CI tool to exchange a short-lived OIDC token for temporary credentials from your KMS (AWS KMS, HashiCorp Vault, or Google Secret Manager).
The biggest challenge in secret management is securing the first secret used to fetch all others. OIDC solves this by using the CI runner's identity as the trust anchor, eliminating the need for a persistent bootstrap secret.
Tradeoff Matrix
| Feature | Env Variables | KMS (Vault/OIDC) |
|---|---|---|
| Complexity | Very Low | Medium/High |
| Auditability | None | Full Logs |
| Blast Radius | High (Persistent) | Low (Ephemeral) |
Conclusion: The 2026 Verdict
If you are building a small internal tool, environment variables might suffice. But for any production-grade application or CI/CD pipeline, the move to a KMS-backed OIDC flow is no longer optional. It reduces the blast radius of a breach, provides a detailed audit trail of who accessed which secret and when, and finally solves the 'Secret Zero' problem that has plagued DevOps for a decade.